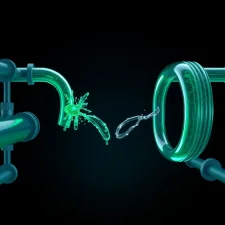
The DeFi ecosystem has been rocked by yet another significant security breach, as Wasabi Protocol became the latest victim of a devastating exploit that drained approximately $4.5 million in user funds. The attack, which leveraged a compromised deployer key lacking essential security safeguards, represents a troubling pattern emerging across decentralized finance platforms. This incident arrives just weeks after Drift Protocol suffered a catastrophic $285 million breach using a nearly identical attack methodology, raising serious questions about fundamental security practices within the industry.
The parallels between these two breaches are striking and deeply concerning for the broader DeFi landscape. Both exploits exploited the same critical vulnerability: an admin key with excessive permissions coupled with a complete absence of protective mechanisms such as timelocks or multisignature requirements. This pattern suggests that many protocols continue to deploy infrastructure with dangerous single points of failure, despite repeated public warnings from security researchers and auditors about the risks associated with centralized administrative controls.
The Anatomy of the Wasabi Protocol Exploit
The Wasabi Protocol attack followed a well-documented playbook that has become disturbingly common in recent DeFi incidents. Attackers gained unauthorized access to the deployer key, a critical administrative credential that typically holds permission to modify core protocol parameters and access to liquidity pools. Unlike properly secured systems, Wasabi Protocol had implemented no protective mechanisms to slow down or prevent the misuse of this key.
Once the attacker gained control of the deployer key, they were able to execute a direct drainage of funds with virtually no friction or delay. The absence of a timelock—a mechanism that requires a waiting period between when an administrative action is initiated and when it takes effect—meant that users and protocol guardians had no opportunity to detect the malicious transaction and intervene. Similarly, the lack of multisignature requirements meant that no secondary approval was necessary to authorize the fund transfer, eliminating a critical check on unauthorized actions.
The $4.5 million loss represents a devastating blow to Wasabi Protocol's users and credibility. However, the incident serves as another data point in an alarming trend: protocols that fail to implement basic security best practices face existential threats to their operations and user trust.
Lessons From Drift Protocol's Larger Breach
The Drift Protocol exploit, which occurred earlier this month and resulted in $285 million in losses, demonstrated the same fundamental vulnerability on a much larger scale. That incident, which shook the DeFi community, involved attackers exploiting a compromised admin key to manipulate prices and drain substantial collateral from the protocol's lending markets. The ease with which such a massive amount of capital could be accessed and removed underscored how critical administrative key security truly is.
What makes the Drift breach particularly instructive is the clarity with which it exposed industry-wide complacency. Despite extensive documentation and community discussion about administrative key risks, Drift had deployed its system without implementing standard protective measures. The incident prompted widespread calls for protocol developers to implement multisignature schemes and timelocks immediately, yet the Wasabi breach suggests these warnings have not been universally heeded.
The timing of the Wasabi incident—following so closely on Drift's much larger breach—suggests that attackers may be systematically targeting protocols with known security gaps. This hunting pattern creates additional urgency for remaining vulnerable protocols to secure their administrative infrastructure before becoming the next victims.
Industry-Wide Security Gaps and Best Practices
The recurring nature of these exploits points to a disturbing reality: many DeFi protocols, particularly those launched with speed prioritized over security, have failed to implement fundamental safeguards that have been understood and recommended for years. Several critical best practices remain underutilized:
- Timelock mechanisms that enforce a delay between when administrative actions are proposed and when they become effective, allowing time for human review and community response
- Multisignature wallets requiring approval from multiple independent signers before critical actions can be executed, eliminating single points of failure
- Governance decentralization that transfers administrative authority from individual developers to distributed token-holder voting systems
- Key management infrastructure that properly segregates different administrative functions and limits the blast radius of any single key compromise
- Regular security audits by reputable firms specializing in smart contract security
These practices are not new innovations—they represent industry consensus on how to properly secure critical financial infrastructure. Yet their inconsistent adoption suggests a gap between knowledge and implementation within the development community.
The Emerging Pattern of Targeted Exploitation
Both the Drift and Wasabi incidents raise an important question: are these exploits the result of security lapses being opportunistically discovered, or are attackers actively targeting known vulnerabilities? The similarities in attack methodology and the temporal proximity of the breaches suggest a more systematic approach to identifying and exploiting unprotected protocols.
This pattern has significant implications for the remaining DeFi ecosystem. Protocols using similar architectural patterns face elevated risk, particularly if their administrative structures remain unprotected. The economic incentive for attackers is substantial—tens of millions of dollars in potential gains create powerful motivation to systematically hunt for vulnerable systems.
The discovery of these vulnerabilities also raises questions about the adequacy of current security auditing practices. Both Drift and Wasabi underwent professional audits, yet critical architectural vulnerabilities remained undetected or were flagged but not remediated. This suggests either that audit standards need strengthening or that protocol teams are ignoring audit recommendations when they conflict with deployment timelines.
Moving Forward: Urgent Security Requirements
The Wasabi Protocol exploit and its parallel to the Drift breach create a critical moment for the DeFi industry. Protocol teams must recognize that security failures are not abstract risks—they have direct, measurable consequences for user funds and ecosystem stability. The following steps should be prioritized:
First, all existing protocols should immediately audit their administrative key structures and implement timelocks and multisignature requirements for critical functions. Second, project teams launching new protocols should establish security requirements that cannot be bypassed for speed of deployment. Third, the community should demand greater transparency about governance structures and administrative permissions, enabling users to make informed decisions about which protocols to trust.
The Wasabi Protocol incident represents more than just another DeFi hack—it represents a systemic failure to implement known protective measures. Until the industry establishes and enforces universal security standards for administrative infrastructure, similar breaches will continue to erode user trust and capital in the DeFi ecosystem.
This article was last reviewed and updated in May 2026.